Read Sonatype’s sixth annual report on open source software development and understand why productivity doesn’t have to come at the cost of reduced security.
The State of the Software Supply Chain 2020 Report combines a broad set of public and proprietary data, along with the results of a survey of more than 5,600 professional developers to reveal significant findings, including:
- 430% growth in next-generation cyberattacks actively targeting OSS (Chapter 1)
- 1.5 trillion requests to download OSS components (Chapter 2)
- 530 times faster to update dependencies for exemplary OSS projects (Chapter 3)
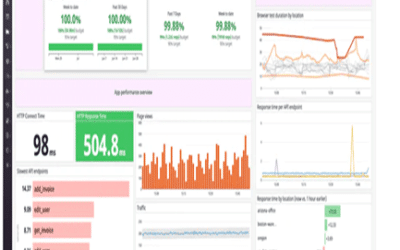
- 26 times faster remediation of vulnerabilities in high-performance equipment (Chapter 4)
- 11% of OSS components used in applications have known vulnerabilities (Chapter 5)
For the second year in a row, Sonatype has collaborated with research partners Gene Kim of IT Revolution and Dr. Stephen Magill CEO of MuseDev, to examine how high-performance enterprise software development teams successfully balance their performance and risk management practices while assembling applications with open source components.
Source: Sonatype