Cybersecurity solutions
for your company

Enterprises improve security of their digital ecosystems when they -deploy controls that provide 360-degree view of their attack surfaces, even though these are increasingly fragmented and complex. Adopting a holistic approach to security architectures helps achieve a secure design.
Gartner predicts that by 2025, 45% of organizations worldwide will have experienced cyberattacks in their software supply chains. There is an impressive increase in AI-driven attacks, and there is the need to be prepared for this new era.
At Panorama IT we recommend:
- Betting on the concept of security by design, and optimizing cybersecurity capabilities with flexible models that foster agility.
- Plan threat detection efforts from an end-to-end view of the attack surface, adopting the mindset of an attacker.
- Training employees to improve and maintain cybersecurity effectiveness by learning how to recognize and avoid these attacks.
At Panorama IT we perform a complete cybersecurity consulting to detect your potential vulnerabilities and propose solutions.
Are you prepared to detect and react to a cyber-attack?
Prevention
Detection
Answer
Discover our cyber-attack prevention services
- Vulnerability analysis and remediation in:
- IT infrastructure
- Multicloud and hybrid environments
- Applications and microservices
- APIs
- Active Directory
- Software Supply Chain Security (DevSecOps)
- Defensive measures for D3FEND framework advised by MITRE and NSA
- PCI
- GDPR (Europe)
- External Circular 007 of 2018 (Colombia)
- Audit and compliance
- Industrial Security / IOT
Learn about our cyber threat detection services
- Ransomware
- Threat Intelligence
- SIEM
- Fraud control and identification
- Identification of anomalous behavior of IT infrastructure elements
- Monitoring of new vulnerabilities in applications and microservices
- Credential theft
- User behavior anomalies
- Network traffic anomalies
- Anomalies in office automation tools (Office 365)
- Non-compliance of compliance in cloud environments
This is how we respond to cyber-attacks
- Automatic software bill of materials (SBOM) listing
- Automatic remediation of vulnerabilities in applications and microservices
- Automation and Orchestration / SOAR
- SOC management and collaboration
”
FAQs

What are the main cyber threats facing an organization?
The main cyber threats may include malware attacks, ransomware, phishing, social engineering, intrusion attempts, software vulnerabilities, and security breaches. To mitigate these risks, it is advisable to rely on cybersecurity services provided by a specialized company that protects your IT infrastructure and provides adequate solutions to address these threats.
How can I protect my systems and networks against malware and ransomware attacks?
To protect your systems and networks against malware and ransomware attacks, it is important to have a strategy based on cybersecurity solutions. In addition, it is crucial to maintain constant observability through monitoring tools and analysis of logs and metrics, which will allow you to detect potential threats and take proactive measures to strengthen the security of your IT infrastructure and mitigate potential risks.
What is the difference between a phishing attack and a social engineering attack?
While phishing relies on forged messages to trick people into divulging personal or financial information, social engineering focuses on manipulating people through human interactions to gain access to valuable information or protected systems. Both types of attacks are dangerous and require increased awareness and cybersecurity measures to protect against them.
What are the key measures to protect a company's network against cyber-attacks?
We would highlight three: Educating and raising staff awareness about cybersecurity , constant monitoring of IT infrastructure and Collaborating with a cybersecurity company that provides specialized services tailored to your company’s needs.
Why is it important to perform vulnerability assessments and penetration tests on a company's systems?
These assessments help identify potential weaknesses and vulnerabilities in your IT infrastructure and cybersecurity. These assessments allow you to take proactive measures to close security gaps and mitigate potential risks, helping protect your company against potential attacks and ensuring the integrity and confidentiality of your data.
Delete
What is the importance of having a cybersecurity incident response plan?
The importance of having a cybersecurity incident response plan lies in an organization’s ability to react quickly and effectively to possible attacks or security breaches in its IT infrastructure. A well-designed plan, supported by a cybersecurity company that provides specialized services, can minimize the impact of incidents, reduce downtime and ensure the recovery and operational continuity of the company.
What steps should I take in the event of a security breach?
In the event of a security breach in the IT infrastructure, it is important to follow these key steps: isolate the affected system, notify the security and IT teams, collect evidence, mitigate the attack and restore the integrity of the affected systems. Subsequently, a thorough review of the breach should be carried out with the support of a cybersecurity company that provides specialized services to prevent future incidents and strengthen the security of the organization.
Our solutions







Splunk is an end-to-end platform that enables future state routing, analytics, and data visualization in your enterprise.
With Splunk we solve many of the most important challenges throughout the entire data lifecycle: searching, monitoring, and analyzing, and integrating them into an easy and intuitive web interface.
Splunk's goal is to make Big Data accessible to the entire organization, enabling pattern identification, measurement, problem diagnosis and intelligence provisioning.
In addition, we provide training and certification services in Splunk technology, to ensure that your team has the necessary skills to use and manage this powerful tool effectively. With Splunk, your company will be prepared to address current and future data analytics challenges.
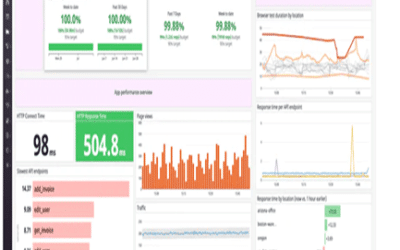
Datadog is a powerful SaaS data analysis platform that replaces multiple monitoring products with a unified solution. Ideal for real-time decision making on your IT infrastructure.
With Datadog we help developers and operations teams see their entire infrastructure (cloud, servers, applications, services, metrics and more) in one place, allowing them to solve problems faster and more efficiently, eliminate communication silos and achieve DevOps goals.
Our platform will allow you to consolidate your monitoring tools into a single intuitive interface, facilitating real-time data collection and visualization.
In addition, we offer training and certification services in Datadog technology, ensuring that your team is properly trained to take full advantage of all its capabilities. With Datadog your company will be equipped with the necessary tools to optimize the monitoring of your IT infrastructure, improve operational efficiency, and ensure business continuity.
Sonatype is open-source management software that focuses on automating and ensuring the security of the entire software supply chain used in application development and services.
As cybersecurity experts, we have a mission to protect digital assets and ensure that software development processes are secure from start to finish. With Sonatype, we provide cybersecurity services that help enhance security and speed in development cycles. Our platform offers comprehensive and efficient management of the software supply chain, allowing the identification and mitigation of risks, vulnerabilities, and threats throughout the application lifecycle.
Additionally, our IT support team is available to provide expert assistance and guidance on the use and configuration of Sonatype, ensuring safe and reliable operation of your IT infrastructure.
Vectra is a powerful real-time threat detection and response platform based on artificial intelligence.
With Vectra, at Panorama IT, we use advanced machine learning algorithms to detect and alert on potential cyberattacks before encryption occurs, drastically reducing response time. Thanks to our Machine Learning algorithms that combine Deep Learning and neural networks, alerts inform you of the attack methods being used in real-time.
Our automated technology based on Vectra allows early and accurate detection of cyber threats, ensuring timely responses to minimize risks and potential damage. We harness the full potential of artificial intelligence to provide greater protection against constantly evolving threats.
The Noname security platform is a comprehensive cybersecurity solution that protects APIs and detects their vulnerabilities in real-time.
APIs were the number one attack vector in 2022, according to Gartner, and they need to be protected. The Noname security platform allows organizations to mitigate this risk, with the ability to connect to any environment (cloud, hybrid, or on-premise).
Noname enables a complete inventory of all APIs, including legacy and shadow APIs, with precise data classification. We identify configuration errors and vulnerabilities in source code, network configuration, and security policies. Additionally, Noname offers runtime protection through behavior-based models, allowing real-time threat detection in APIs.
To ensure maximum security, we provide automated and semi-automated blocking and correction of identified threats. We also conduct continuous vulnerability testing on APIs, allowing us to identify and mitigate risks before they become issues. With automated and dynamic testing development, Noname ensures seamless integration into existing IT infrastructure.
As a cybersecurity company, at Panorama IT, we provide robust IT support and ensure that our customers always receive assistance.
Lacework is a cybersecurity platform and automatic anomaly detection that provides visibility, context, and security in a multi-cloud environment, all from a single platform.
With Lacework, we harness the potential of machine learning, behavior analysis, and anomaly detection to discover threats, misconfigurations, and outliers in environments such as Amazon Web Services, Microsoft Azure, Google Cloud, workloads, containers, and Kubernetes.
The Polygraph data platform can identify and alert on potential risks and vulnerabilities in real-time. With Lacework, we can help you optimize your cloud security strategy, improve compliance, facilitate incident investigation, and reduce the workload of your security and DevOps teams.
Trust Panorama IT's cybersecurity services to protect your assets in the cloud and ensure a secure and reliable environment for your digital operations.
Tenable is a cybersecurity platform that provides broad visibility into cyber risk, including on-premises IT infrastructure, Active Directory, and the cloud environment.
Tenable is the world's first Cyber Exposure platform and a pioneer in the IT vulnerability management market.
With Tenable, we ensure your cloud, containers, OT devices, and traditional IT assets are secure. It provides in-depth analysis that allows you to make more informed security decisions. With Tenable, you can identify and assess vulnerabilities and threats in your IT infrastructure and gain a clear view of the risks you face.
Panorama IT's cybersecurity services are designed to help organizations strengthen their security posture and efficiently protect their digital assets.
Related news
The essential safety guide
Do you have a cybersecurity...
5 keys for CISOs to accelerate business.
Now more than ever, chief...
What most people don’t know about Synthetic Monitoring
Synthetic monitoring enables...