Last May 5th we had a Round Table session with Sonatype, where members of the security, development and DevOps areas of some important companies in Spain participated.
We talked about trends in DevSecOps, the relationship between development and security areas and about current tools to support management.
Below, we would like to share some conclusions:
About trends in DevSecOps:
- Rapid development is required due to market demands.
- Attacks are being made on the supply chain, compromising the projects generated by third-party dependencies
- The use of containers and supplies
- The use of infrastructure as code
On the relationship between development and security areas:
- Developers need to be able to be included at the function level and assess security when they are in the development process
- Vulnerability scanning of the application is done when it is finished, if any is found, they have to remanufacture causing rework.
- It is important the culture of collaboration and teamwork between the two areas, that the security areas know more and more how the applications are developed and their checkpoints.
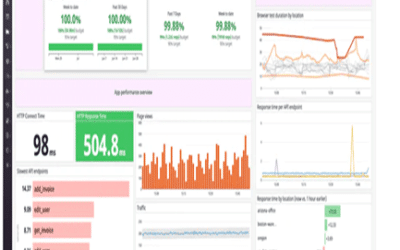
Regarding the current tools to help in management:
- Sometimes tools are imposed that developers are reluctant to use.
- There are tools that generate too much noise and some choose to ignore them.
- They do not use a tool that integrates the security phase throughout their development cycle.
Sonatype was created to help mitigate security risks at an early stage, securing the entire supply chain. As well as, to support developers and security areas to work very well together.
As partners, Panorama Technologies can help you find the solution to save time and money on rework, to comply with security policies without affecting application development agility, and to help forge a smooth relationship between security and development teams.